Foreign intelligence services view university students not as political actors, but as low-cost, high-yield assets within a long-term information supply chain. This systematic targeting, recently highlighted by Chinese state security warnings, relies on a predictable economic and psychological framework designed to bypass traditional security heuristics. The recruitment process is a calculated arbitrage of a student’s immediate financial precariousness against the future value of their academic or professional access.
The Triad of Asset Selection
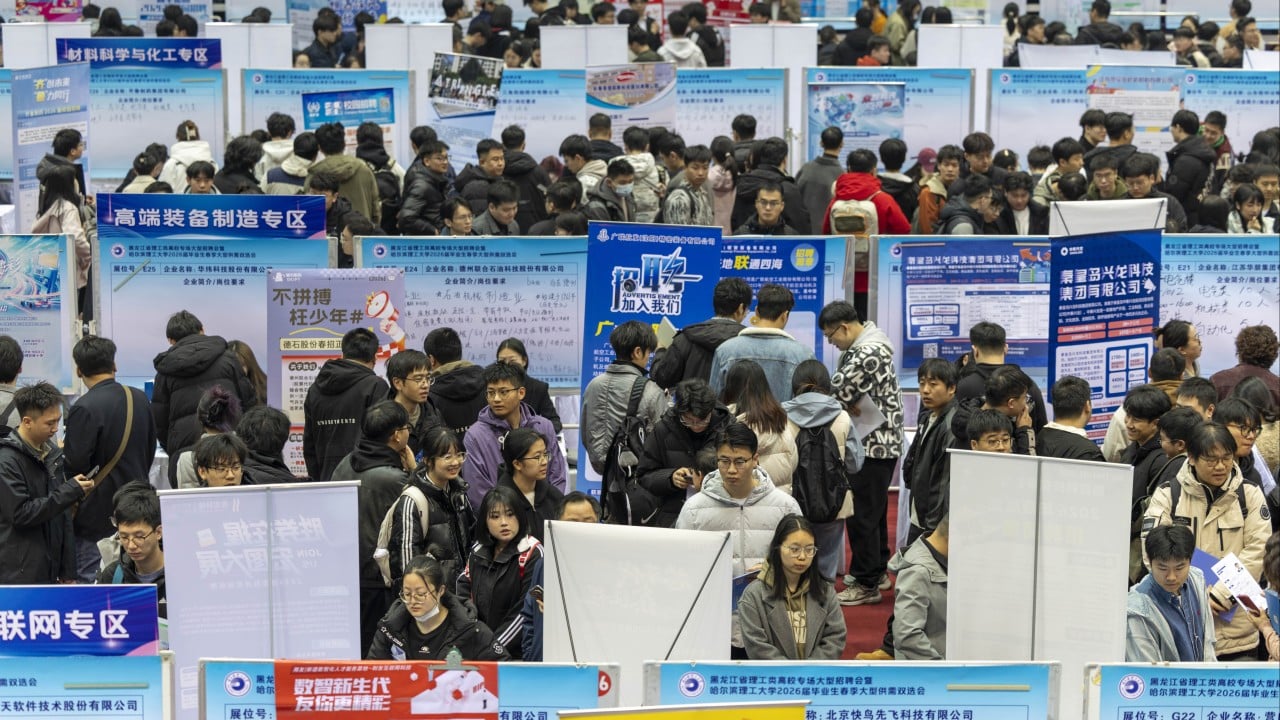
State security apparatuses identify targets based on a specific intersection of variables. The recruitment of students follows a clear logic of "early-stage acquisition." Intelligence officers are not looking for someone who currently holds state secrets; they are looking for "seedlings"—individuals who, in five to ten years, will occupy roles in sensitive research labs, government bureaus, or defense contractors.
1. Data-Driven Prospecting
Recruitment begins with a massive filtering of public digital footprints. Spies analyze LinkedIn profiles, academic publications, and social media activity to find students in high-value sectors: quantum computing, semiconductors, biotechnology, and maritime engineering. The objective is to find high-performing individuals who exhibit signs of financial stress or a lack of institutional loyalty.
2. The Credibility Gap
Espionage rarely presents itself as such during the initial contact. It is disguised as legitimate market research, data analysis consulting, or academic collaboration. This is the "grey zone" of intelligence work. By framing the interaction as a professional opportunity, the recruiter lowers the target’s psychological barriers. The student perceives the relationship as a meritocratic reward rather than a subversive act.
3. Geographic and Institutional Arbitrage
Students at elite institutions or those studying abroad are prioritized. These individuals represent a bridge between disparate geopolitical systems. A student from a sensitive home nation studying at a high-ranking foreign university is a dual-value asset: they possess domestic cultural capital and foreign technical exposure.
The Economic Model of the High Pay Trap
The core mechanism of student recruitment is the "disproportionate compensation" model. When a foreign entity offers thousands of dollars for a "literature review" or "basic data collection" that should realistically cost a fraction of that amount, they are not paying for the work. They are paying for the precedent of transaction.
Financial Hooking and Sunk Cost
The initial payment creates a financial dependency. Once a student accepts money for a seemingly benign task, the power dynamic shifts. The recruiter then introduces slightly more sensitive requests. If the student balks, the recruiter utilizes the previous payments as leverage, implying that the student has already crossed a legal line. This is a classic application of the sunk cost fallacy, where the individual continues a dangerous path because they have already invested their reputation.
The Cost of Acquisition vs. Maintenance
For an intelligence agency, a student is a cheap asset. Maintaining a career spy is expensive and high-risk. Cultivating a student requires only a few thousand dollars in "consulting fees" and minimal operational overhead. Even if the student fails to reach a position of power, the financial loss to the agency is negligible. If they succeed, the return on investment is exponential.
Structural Vulnerabilities in Academic Environments
The university system possesses inherent structural flaws that intelligence services exploit. The culture of open collaboration and the "publish or perish" mentality creates a friction-less environment for information harvesting.
The Illusion of Open Source
Many students believe that since they are working on "unclassified" or "basic research," there is no harm in sharing it. This ignores the concept of Information Mosaic Theory. In espionage, a single piece of unclassified data is worthless, but when combined with a thousand other pieces of unclassified data, it reveals a classified picture of a nation’s technological trajectory. Students are effectively providing the missing tiles in a mosaic they cannot see.
Lack of Counter-Intelligence Literacy
Traditional education focuses on technical proficiency but ignores operational security (OPSEC). Students are trained to be experts in physics or AI, but they are rarely trained to recognize the signs of social engineering. This "competence asymmetry" makes them easy prey for professional manipulators who have spent decades perfecting the art of the "soft approach."
The Psychology of the Gradual Slide
Recruitment is a process of incremental compromise. No one is asked to steal a hard drive on day one. The "Gradual Slide" operates through three distinct psychological phases:
- The Professional Validation Phase: The recruiter acts as a mentor or a fan of the student’s work. They provide ego-stroking feedback and financial rewards that the university system often lacks.
- The Information Testing Phase: The student is asked for non-sensitive but proprietary information, such as internal seminar notes or the names of colleagues working on specific projects. This tests the student's willingness to violate minor rules.
- The Coercive Pivot: Once the student is sufficiently entangled—either through significant financial receipts or documented rule-breaking—the "mask" is dropped. The recruiter reveals their true affiliation or makes it clear that the student is now an agent of influence.
Quantifying the Risk to National Security
The impact of student recruitment is not felt in the short term. It is a "latent threat." The damage manifests years later when the recruited student enters the workforce.
- Technology Leakage: The unauthorized transfer of intellectual property (IP) before it can be patented or protected by national security protocols.
- Personnel Compromise: A compromised student can act as a "talent spotter," identifying other vulnerable peers for recruitment, creating a self-sustaining network of assets within a single institution.
- Policy Subversion: Over time, individuals in government roles who were recruited as students may subtly influence policy decisions to favor the interests of a foreign power.
Strategic Defense and Institutional Hardening
Addressing this threat requires moving beyond simple warnings and into a regime of structural resilience. Universities and government bodies must treat student protection as a component of research integrity.
Implementing Mandatory OPSEC Training
High-value departments (STEM, International Relations, Defense Economics) must integrate operational security into their curricula. This training should not be a "don't talk to strangers" lecture, but a rigorous breakdown of social engineering tactics, the legality of foreign consulting, and the reporting mechanisms for suspicious contacts.
Financial Transparency Protocols
Universities should implement disclosure requirements for students receiving significant foreign funding or "consulting" fees. By normalizing the reporting of external income, institutions can identify outliers who may be in the early stages of recruitment. This is not about surveillance; it is about creating a "paper trail" that serves as a deterrent to recruiters who rely on secrecy.
The Role of De-Stigmatization
One of the greatest tools a recruiter has is the student's fear of getting in trouble. If a student realizes they have made a mistake, they are often too terrified to report it to authorities, fearing expulsion or prosecution. Institutions must create "safe harbor" policies where students can report suspicious contacts or accidental compromises without facing immediate punitive action. This breaks the recruiter's primary leverage: the threat of exposure.
The geopolitical landscape of 2026 demands a shift in how we perceive the academic-industrial complex. The university is no longer a sanctuary of pure thought; it is a primary theater of information warfare. Protecting students requires a cold-eyed assessment of their value as assets and a proactive strengthening of the psychological and procedural barriers that prevent their exploitation. The goal is to increase the "cost of acquisition" for foreign spies to a point where the student recruitment model becomes economically and operationally non-viable.
Establish a centralized, non-punitive reporting office for foreign solicitations within all state-funded research universities. Require all students handling dual-use technology research to undergo "Grey Zone Awareness" certification. Shift the defensive posture from reactive warnings to a standardized risk-management framework that treats intellectual capital as a physical asset requiring constant, layered protection.